Releases: opf/openproject
OpenProject 17.2.2
Release date: 2026-03-17
We released OpenProject OpenProject 17.2.2.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Bug fixes and changes
OpenProject 17.2.1
Release date: 2026-03-16
We released OpenProject OpenProject 17.2.1.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-32698 - SQL Injection via Custom Field Name can be chained to Remote Code Execution
OpenProject is vulnerable to an SQL injection attack via a custom field's name. When that custom field was used in a Cost Report, the custom field's name was injected into the SQL query without proper sanitation. This allowed an attacker to execute arbitrary SQL commands during the generation of a Cost Report.
As custom fields can only be generated by users with full administrator privileges, the attack surface is somewhat reduced.
Together with another bug in the Repositories module, that used the project identifier without sanitation to generate the checkout path for a git repository in the filesystem, this allowed an attacker to checkout a git repository to an arbitrarily chosen path on the server. If the checkout is done within certain paths within the OpenProject application, upon the next restart of the application, this allows the attacker to inject ruby code into the application.
As the project identifier cannot be manually edited to any string containing special characters like dots or slashes, this needs to be changed via the SQL injection described above.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jqhf-rf9x-9rhx
CVE-2026-32703 - Repository files are served with the MIME type allowing them to be used to bypass Content Security Policy
When using the Repositories module in a project, it was possible to access the raw files via the browser with a URL like /projects/{project}/repository/revisions/{commit_id}/raw/{file}.js.raw. For those files, the MIME type was detected via the filename extension. For JavaScript and CSS files those files were then served from the same domain name as the application with the correct MIME type for active content and could be used to bypass the Content Security Policy. Together with other areas, where unsanitized HTML was served, this allowed persistent XSS attacks.
The MIME type detection for Repository files has been removed and files are served as application/octet-stream which will block their execution via the Content Security Policy.
Two places that could be used to abuse this vulnerability have been fixed:
The Repositories module did not properly escape filenames displayed from repositories. This allowed an attacker with push access into the repository to create commits with filenames that included HTML code that was injected in the page without proper sanitation. This allowed a persisted XSS attack against all members of this project that accessed the repositories page to display a changeset where the maliciously crafted file was deleted.
When a work package name contains HTML content and the work package is attached to a meeting, the work package name is rendered in the activities feed without proper sanitation.
All of those vulnerabilities were reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p423-72h4-fjvp
Bug fixes and changes
- Bugfix: Screenshot overlaps with CKeditor tool bar when scrolling [#72678]
- Bugfix: Jira import: error when imported type is the same as on OP (with mandatory custom fields) [#72854]
- Bugfix: Nextcloud: When creating an AMPF folder fails, other folders are also not created [#72940]
- Bugfix: Send test email fails when using SMTP and TLS [#73099]
- Bugfix: curl removed from openproject/openproject:17-slim in 17.2.0 [#73142]
Contributions
A big thanks to our Community members for reporting bugs and helping us identify and provide fixes.
This release, special thanks for reporting and finding bugs go to Martin Pfister.
OpenProject 17.1.3
Release date: 2026-03-16
We released OpenProject OpenProject 17.1.3.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-32698 - SQL Injection via Custom Field Name can be chained to Remote Code Execution
OpenProject is vulnerable to an SQL injection attack via a custom field's name. When that custom field was used in a Cost Report, the custom field's name was injected into the SQL query without proper sanitation. This allowed an attacker to execute arbitrary SQL commands during the generation of a Cost Report.
As custom fields can only be generated by users with full administrator privileges, the attack surface is somewhat reduced.
Together with another bug in the Repositories module, that used the project identifier without sanitation to generate the checkout path for a git repository in the filesystem, this allowed an attacker to checkout a git repository to an arbitrarily chosen path on the server. If the checkout is done within certain paths within the OpenProject application, upon the next restart of the application, this allows the attacker to inject ruby code into the application.
As the project identifier cannot be manually edited to any string containing special characters like dots or slashes, this needs to be changed via the SQL injection described above.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jqhf-rf9x-9rhx
CVE-2026-32703 - Repository files are served with the MIME type allowing them to be used to bypass Content Security Policy
When using the Repositories module in a project, it was possible to access the raw files via the browser with a URL like /projects/{project}/repository/revisions/{commit_id}/raw/{file}.js.raw. For those files, the MIME type was detected via the filename extension. For JavaScript and CSS files those files were then served from the same domain name as the application with the correct MIME type for active content and could be used to bypass the Content Security Policy. Together with other areas, where unsanitized HTML was served, this allowed persistent XSS attacks.
The MIME type detection for Repository files has been removed and files are served as application/octet-stream which will block their execution via the Content Security Policy.
Two places that could be used to abuse this vulnerability have been fixed:
The Repositories module did not properly escape filenames displayed from repositories. This allowed an attacker with push access into the repository to create commits with filenames that included HTML code that was injected in the page without proper sanitation. This allowed a persisted XSS attack against all members of this project that accessed the repositories page to display a changeset where the maliciously crafted file was deleted.
When a work package name contains HTML content and the work package is attached to a meeting, the work package name is rendered in the activities feed without proper sanitation.
All of those vulnerabilities were reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p423-72h4-fjvp
Bug fixes and changes
OpenProject 17.0.6
Release date: 2026-03-16
We released OpenProject OpenProject 17.0.6.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-32698 - SQL Injection via Custom Field Name can be chained to Remote Code Execution
OpenProject is vulnerable to an SQL injection attack via a custom field's name. When that custom field was used in a Cost Report, the custom field's name was injected into the SQL query without proper sanitation. This allowed an attacker to execute arbitrary SQL commands during the generation of a Cost Report.
As custom fields can only be generated by users with full administrator privileges, the attack surface is somewhat reduced.
Together with another bug in the Repositories module, that used the project identifier without sanitation to generate the checkout path for a git repository in the filesystem, this allowed an attacker to checkout a git repository to an arbitrarily chosen path on the server. If the checkout is done within certain paths within the OpenProject application, upon the next restart of the application, this allows the attacker to inject ruby code into the application.
As the project identifier cannot be manually edited to any string containing special characters like dots or slashes, this needs to be changed via the SQL injection described above.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jqhf-rf9x-9rhx
CVE-2026-32703 - Repository files are served with the MIME type allowing them to be used to bypass Content Security Policy
When using the Repositories module in a project, it was possible to access the raw files via the browser with a URL like /projects/{project}/repository/revisions/{commit_id}/raw/{file}.js.raw. For those files, the MIME type was detected via the filename extension. For JavaScript and CSS files those files were then served from the same domain name as the application with the correct MIME type for active content and could be used to bypass the Content Security Policy. Together with other areas, where unsanitized HTML was served, this allowed persistent XSS attacks.
The MIME type detection for Repository files has been removed and files are served as application/octet-stream which will block their execution via the Content Security Policy.
Two places that could be used to abuse this vulnerability have been fixed:
The Repositories module did not properly escape filenames displayed from repositories. This allowed an attacker with push access into the repository to create commits with filenames that included HTML code that was injected in the page without proper sanitation. This allowed a persisted XSS attack against all members of this project that accessed the repositories page to display a changeset where the maliciously crafted file was deleted.
When a work package name contains HTML content and the work package is attached to a meeting, the work package name is rendered in the activities feed without proper sanitation.
All of those vulnerabilities were reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p423-72h4-fjvp
Bug fixes and changes
OpenProject 16.6.9
Release date: 2026-03-16
We released OpenProject OpenProject 16.6.9.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-32698 - SQL Injection via Custom Field Name can be chained to Remote Code Execution
OpenProject is vulnerable to an SQL injection attack via a custom field's name. When that custom field was used in a Cost Report, the custom field's name was injected into the SQL query without proper sanitation. This allowed an attacker to execute arbitrary SQL commands during the generation of a Cost Report.
As custom fields can only be generated by users with full administrator privileges, the attack surface is somewhat reduced.
Together with another bug in the Repositories module, that used the project identifier without sanitation to generate the checkout path for a git repository in the filesystem, this allowed an attacker to checkout a git repository to an arbitrarily chosen path on the server. If the checkout is done within certain paths within the OpenProject application, upon the next restart of the application, this allows the attacker to inject ruby code into the application.
As the project identifier cannot be manually edited to any string containing special characters like dots or slashes, this needs to be changed via the SQL injection described above.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jqhf-rf9x-9rhx
CVE-2026-32703 - Repository files are served with the MIME type allowing them to be used to bypass Content Security Policy
When using the Repositories module in a project, it was possible to access the raw files via the browser with a URL like /projects/{project}/repository/revisions/{commit_id}/raw/{file}.js.raw. For those files, the MIME type was detected via the filename extension. For JavaScript and CSS files those files were then served from the same domain name as the application with the correct MIME type for active content and could be used to bypass the Content Security Policy. Together with other areas, where unsanitized HTML was served, this allowed persistent XSS attacks.
The MIME type detection for Repository files has been removed and files are served as application/octet-stream which will block their execution via the Content Security Policy.
Two places that could be used to abuse this vulnerability have been fixed:
The Repositories module did not properly escape filenames displayed from repositories. This allowed an attacker with push access into the repository to create commits with filenames that included HTML code that was injected in the page without proper sanitation. This allowed a persisted XSS attack against all members of this project that accessed the repositories page to display a changeset where the maliciously crafted file was deleted.
When a work package name contains HTML content and the work package is attached to a meeting, the work package name is rendered in the activities feed without proper sanitation.
All of those vulnerabilities were reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p423-72h4-fjvp
Bug fixes and changes
OpenProject 17.2.0
Release date: 2026-03-11
We released OpenProject OpenProject 17.2.0.
The release contains several bug fixes and we recommend updating to the newest version.
In these Release Notes, we will give an overview of important feature changes. At the end, you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-30234 - OpenProject BIM BCF XML Import: Path Traversal Leads to Arbitrary Local File Read (AFR)
An authenticated project member with BCF import permissions can upload a crafted .bcf archive where the <Snapshot> value in markup.bcf is manipulated to contain an absolute or traversal local path (for example: /etc/passwd or ../../../../etc/passwd).
During import, this untrusted <Snapshot> value is used as file.path during attachment processing.
As a result, local filesystem content can be read outside the intended ZIP scope.
This results in an Arbitrary File Read (AFR) within the read permissions of the OpenProject application user.
This vulnerability was reported independently by users sam91281 and DQH1 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-q8c5-vpmm-xrxv
CVE-2026-30235 - Business Logic Error on OpenProject through hyperlinks in markdown using DOM clobbering
This vulnerability occurs due to improper validation of OpenProject’s Markdown rendering, specifically in the hyperlink handling. This allows an attacker to inject malicious hyperlink payloads that perform DOM clobbering. DOM clobbering can crash or blank the entire page by overwriting native DOM functions with HTML elements, causing critical JavaScript calls to throw runtime errors during application initialization and halt further execution.
This vulnerability was reported by user frozzipies as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-9rv2-9xv5-gpq8
CVE-2026-30236 - Users that are not project members can be used to calculate Labor Budget, leaking their global hourly rate
When editing a project budget and planning the labor cost, it was not checked that the user that was planned in the budget is actually a project member. This exposed the user's default rate (if one was set up) to users that should only see that information for project members.
Also, the endpoint that handles the pre-calculation for the frontend to display a preview of the costs, while it was being entered, did not properly validate the membership of the user as well. This also allowed to calculate costs with the default rate of non-members.
This vulnerability was reported by user Thesecret2055 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p747-569x-3v3f
CVE-2026-30239 - Permission Check bypass on Budget deletion allows reassignment of WorkPackages into other budgets
When budgets are deleted, the work packages that were assigned to this budget need to be moved to a different budget. This action was performed before the permission check on the delete action was executed. This allowed all users in the application to delete work package budget assignments.
This vulnerability was reported by user cavid as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-gpvh-g967-g4h8
CVE-2026-31974 - Blind SSRF on OpenProject instance via webhooks, and through /admin/test_email via POST request leads to internal network reconnaissance
OpenProject SMTP test endpoint (POST /admin/settings/mail_notifications) accepts arbitrary host and port values and exhibits measurable differences in response behaviour depending on whether the target IP exists and whether the port is open. An attacker with access can use these timing and error distinctions to map internal hosts and identify which services/ports are reachable.
Similarly, you can create webhooks in OpenProject and point them to arbitrary IPs, resulting in the same kind of SSRF issue which allows attackers to scan the internal network.
This vulnerability was reported by user drak3hft7 and adilburak as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-9wr7-j98g-2jh3
Important feature changes
Take a look at our release video showing the most important features introduced in OpenProject 17.2.0:
Release video of OpenProject 17.2
MCP Server (Enterprise add-on)
OpenProject 17.2 introduces the MCP Server, a new Enterprise add-on that lays the foundation for robust integrations between OpenProject and AI systems, including large language models (LLMs), as well as other tools that use the Model Context Protocol (MCP). This server exposes OpenProject's APIv3 resources as MCP-compatible endpoints and enables secure, authenticated access for clients such as LLMs or other MCP clients, opening the door to richer contextual interactions with your project data.
Included in this release are administrative UI support for configuring the MCP Server, infrastructure and metadata endpoints, and integration of MCP authentication with OpenProject’s OAuth2 and API key mechanisms, including external OpenID Connect providers. An initial set of MCP tools and resources is provided to surface key entities (projects, work packages, users, etc.), and response formats can be adjusted based on your preferences. With session-cookie and bearer-token support, the MCP Server acts as a secure bridge between your OpenProject instance and external systems that operate via MCP.
See the MCP Server documentation for setup and examples.
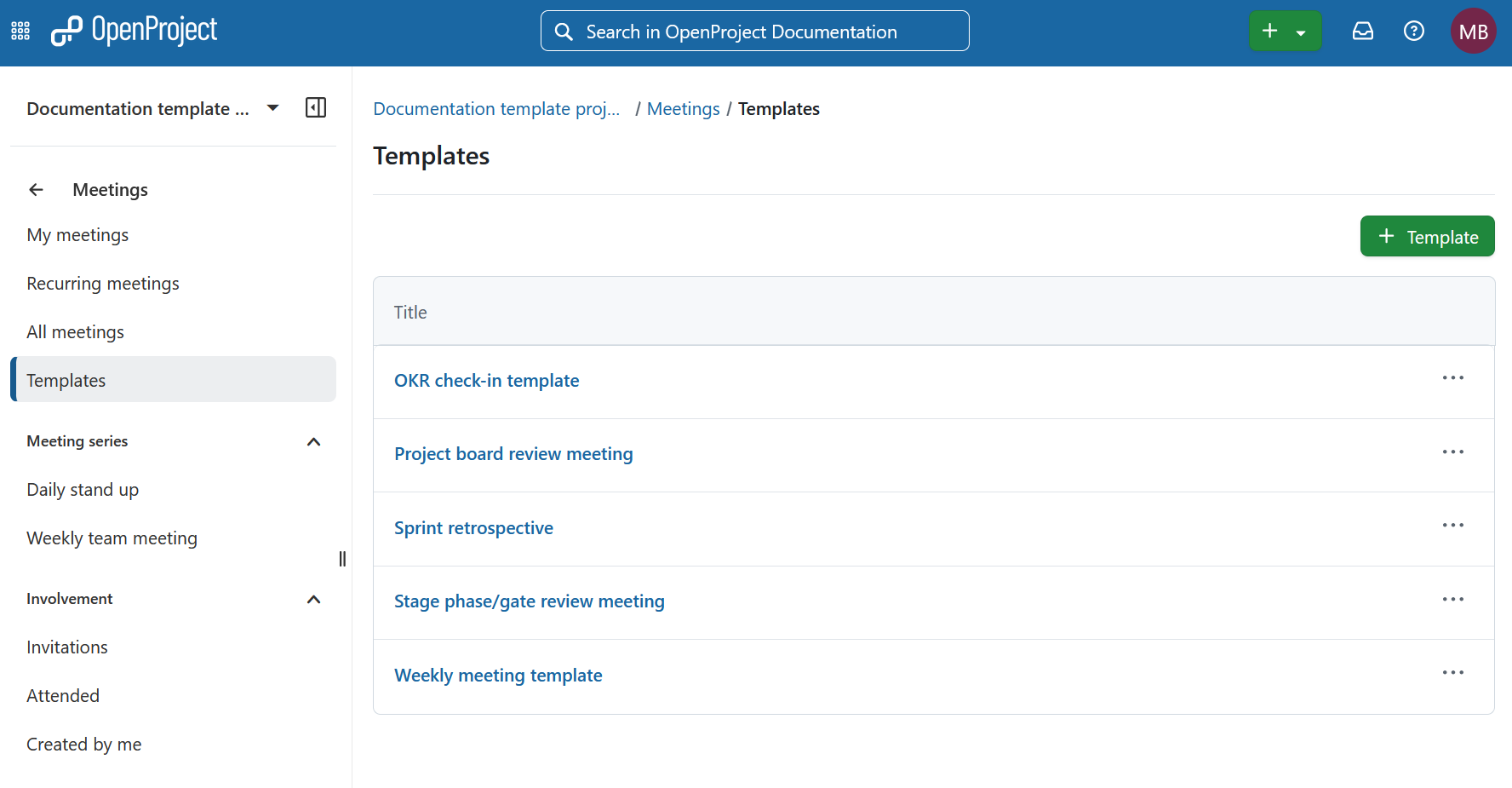
Reusable meeting templates (Enterprise add-on)
Preparing meetings often involves recreating the same agenda structure again and again. With OpenProject 17.2, administrators can now define reusable meeting templates that provide a predefined agenda layout for their teams.
These templates make it easy to start meetings with a proven structure instead of building the agenda from scratch each time. Even when meetings are not held regularly, teams can reuse well-designed formats that guide discussions and help ensure that important topics are addressed.
When creating a new one-time meeting, users can choose from the available templates to automatically populate the agenda with the predefined sections and items. This saves time during setup and promotes alignment across teams.
For more details, please refer to the Meetings documentation.
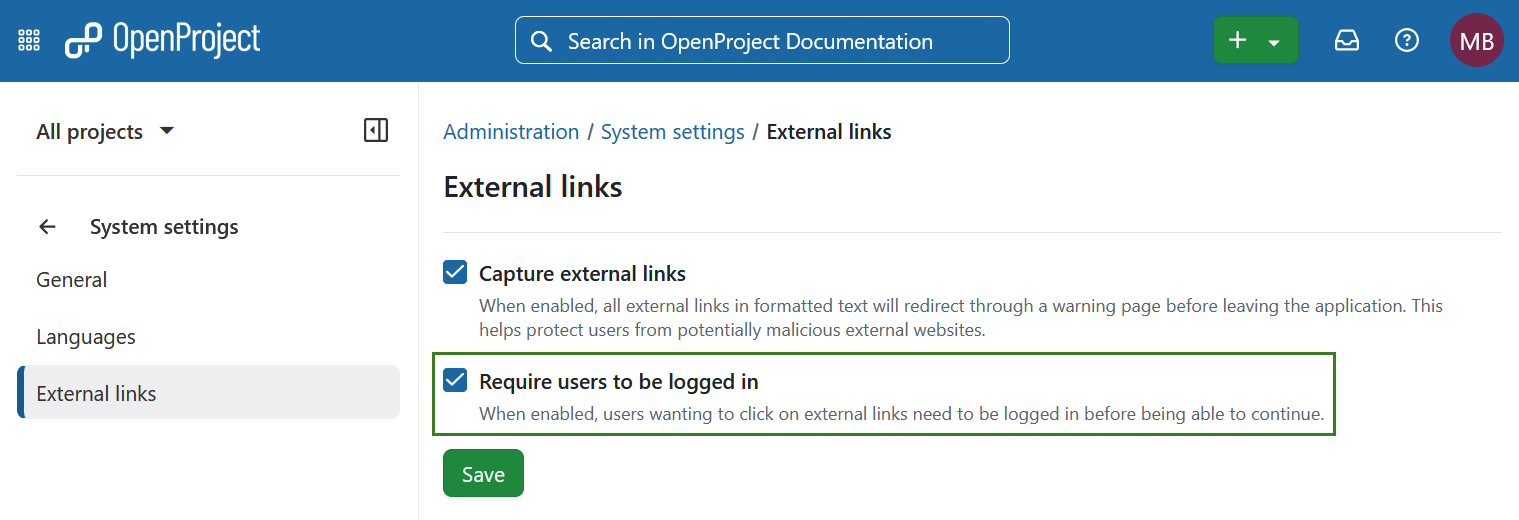
Allow requiring to be logged in to open external links (Enterprise add-on)
Building on the external link safety options introduced in OpenProject 17.1, we’re expanding the protection capabilities in 17.2 to give administrators stronger safeguards for user interactions with links that lead outside of OpenProject.
Administrators can now require users to be logged in before following external links. When this setting is enabled, anyone who is not authenticated will be redirected to the login page before being allowed to continue to the external destination.
Read more about capturing external links in OpenProject.
Project Overview page improvements
OpenProject 17.2 enhances the Project Overview to provide clearer financial insights, easier inline editing, and improved accessibility. Together, these updates make the Overview page a more powerful and inclusive central hub for project information.
Updated Overview widgets for Budgets
Project, program, and portfolio managers can now see key financial indicators at a glance. New budget widgets display planned budget, actual costs, spent ratio, and remaining budget, along with visual breakdowns by cost type and recent monthly actuals. Data is automatically aggregated across subprojects where app...
OpenProject 17.1.2
Release date: 2026-02-26
We released OpenProject OpenProject 17.1.2.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-27715 - User mentions result in information disclosure of user names
The Work Package Activity comment feature does not properly validate whether a mentioned user is a member of the current project.
By manipulating the data-id attribute of the <mention> element in the comment request, a low-privileged user who has access to a single project can mention arbitrary users within the same organization, even if those users are not members of the project.
The backend accepts the supplied user ID without enforcing project membership checks, resolves the mention, and triggers server-side notification workflows (including email notifications).
This behavior violates the intended access control and project isolation model.
This vulnerability was reported by user slashx0x as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-j4m9-7hff-8qgr
CVE-2026-27716 - Information disclosure on OpenProject through /api/v3/custom_fields/{id}/items
The api implementation for custom_fields lacks any validation that the current user is authorized on any project using the custom_field data. This leaks potentially sensitive, project specific business logic.
This vulnerability was reported by user syndrome_impostor as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-qpg6-635j-wjc2
CVE-2026-27717 - IDOR on OpenProject allows any user to overwrite any sprint/version title
An attacker can overwrite the Sprint/Version titles of any project in the same instance/using the same database.
This vulnerability was reported by user posisec as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p3hw-5g6p-69f2
CVE-2026-27718 - Stored HTML Injection via MentionFilter Bypass Leads to Credential Harvesting in Email Notifications
A stored HTML injection vulnerability exists in OpenProject's Markdown rendering pipeline. The MentionFilter decodes HTML entities after the SanitizationFilter has already run, allowing an attacker to inject arbitrary HTML into work package comments. This HTML is stored server-side and rendered without sanitization in email notifications sent to all watchers, assignees, and mentioned users, causing confusion about inserted elements.
This vulnerability was reported by user s-sploit-c as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-cxm3-9m5g-9cq4
CVE-2026-27719 - Authorization flaw in API grids endpoint leads to erase another user widget
The vulnerability is an IDOR/authorization flaw in the My Page grid widgets that allows any authenticated user to delete arbitrary queries by ID. The My Page widgets for work packages accept a queryId inside the widget options. This queryId is stored without any permission checks, and when the widget is removed, a server-side after_destroy hook deletes the query referenced by that queryId.
This vulnerability was reported by user Edia_r as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-7xv7-73x4-qqvp
CVE-2026-27720 - IDOR on backlog stories allows leaking of work package subject
The RbStoriesController calls Story.find(params[:id]) without scoping to the current project or visibility.
By causing an update to the Story with a subject longer than 255 characters, the update is rejected, which results in the original title being returned in the HTTP response.
Since user stories are mapped to work packages[1], this allows reading out the title of any work package just by providing the incrementing work package ID.
This vulnerability was reported by user posisec as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xfmm-g339-3x85
CVE-2026-27721 - Improper Authentication on OpenProject through /oauth/authorize via GET parameter "redirect_uri" when using mobile OAuth app
OpenProject permits the registration of custom URI schemes (e.g., openprojectapp://) for OAuth callbacks without enforcing PKCE (Proof Key for Code Exchange) or validating the exclusivity of the destination application (via Universal Links).
By intercepting this code, an attacker with access to the mobile device can exchange it for an access token (as the client is "Public" and has no secret), effectively hijacking the user's session and gaining full API access to their account
This vulnerability was reported by user wayward as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-w92f-h4wh-g4w4
CVE-2026-27722 - IDOR on OpenProject through /meetings/{meeting_id}/agenda_items/{id}/move_to_section via POST request
There is an Insecure Direct Object Reference (IDOR) in the MeetingAgendaItemsController#move_to_section endpoint. This allows an authenticated user to perform Meeting Agenda Pollution by moving their own agenda items into any meeting section of any other project.
While the initial agenda item is loaded from the authorized meeting context, the controller fails to validate that the target meeting_section_id belongs to the same project or a project where the user has permission.
This vulnerability was reported by user Herdiyan Adam Putra (herdiyanitdev) as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xw8w-4qxm-g9gv
CVE-2026-27731 - IDOR on OpenProject via PUT /work_packages/[workPackageId]/activities/[activityId]/toggle_reaction allows reader user to read internal comments
A missing permission check on the endpoint to add an emoji reaction to a comment allows an attacker to add an emoji reaction to internal comments, even if they do not have access to internal comments. To correctly display the information in the frontend, the server returns the complete internal comment with the added emoji reaction to the attacker. This allows the attacker by guessing the ID of an internal comment, to access those comments without the permission to see them.
This vulnerability was reported by user tuannq_gg as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-3qgp-q2x5-c4jw
CVE-2026-27733 - Authorization bypass via MCP endpoint
If the MCP server is enabled in the application, users that do not have access to enumerate Status or Types could access those resources without proper permission checks via the MCP server.
This vulnerability was reported by users noidont and syndrome_impostor as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-w9w6-f59w-89vj
CVE-2026-27817 - Missing boundary check allows users with Manage Agenda Items permission in one project to create Agenda Items in Meetings in other projects
When creating meeting agenda items, the code did properly check that the section an agenda item should be put into belongs to the meeting provided in the URL. This lead to a user with the Manage Meeting Agendas permission in one project to be able to add meeting agenda items to every meeting in the instance. Together with the response about the creation of the meeting agenda item, certain meeting details including
-
Status of the meeting
-
Creator of the meeting
-
Date and Time range of the meeting
No other details of the meeting information were exposed.
This vulnerability was reported by user sam91281 as part of the [YesWeHack.com OpenProject...
OpenProject 17.0.5
Release date: 2026-02-26
We released OpenProject OpenProject 17.0.5.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-27715 - User mentions result in information disclosure of user names
The Work Package Activity comment feature does not properly validate whether a mentioned user is a member of the current project.
By manipulating the data-id attribute of the <mention> element in the comment request, a low-privileged user who has access to a single project can mention arbitrary users within the same organization, even if those users are not members of the project.
The backend accepts the supplied user ID without enforcing project membership checks, resolves the mention, and triggers server-side notification workflows (including email notifications).
This behavior violates the intended access control and project isolation model.
This vulnerability was reported by user slashx0x as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-j4m9-7hff-8qgr
CVE-2026-27716 - Information disclosure on OpenProject through /api/v3/custom_fields/{id}/items
The api implementation for custom_fields lacks any validation that the current user is authorized on any project using the custom_field data. This leaks potentially sensitive, project specific business logic.
This vulnerability was reported by user syndrome_impostor as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-qpg6-635j-wjc2
CVE-2026-27717 - IDOR on OpenProject allows any user to overwrite any sprint/version title
An attacker can overwrite the Sprint/Version titles of any project in the same instance/using the same database.
This vulnerability was reported by user posisec as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-p3hw-5g6p-69f2
CVE-2026-27718 - Stored HTML Injection via MentionFilter Bypass Leads to Credential Harvesting in Email Notifications
A stored HTML injection vulnerability exists in OpenProject's Markdown rendering pipeline. The MentionFilter decodes HTML entities after the SanitizationFilter has already run, allowing an attacker to inject arbitrary HTML into work package comments. This HTML is stored server-side and rendered without sanitization in email notifications sent to all watchers, assignees, and mentioned users, causing confusion about inserted elements.
This vulnerability was reported by user s-sploit-c as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-cxm3-9m5g-9cq4
CVE-2026-27719 - Authorization flaw in API grids endpoint leads to erase another user widget
The vulnerability is an IDOR/authorization flaw in the My Page grid widgets that allows any authenticated user to delete arbitrary queries by ID. The My Page widgets for work packages accept a queryId inside the widget options. This queryId is stored without any permission checks, and when the widget is removed, a server-side after_destroy hook deletes the query referenced by that queryId.
This vulnerability was reported by user Edia_r as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-7xv7-73x4-qqvp
CVE-2026-27720 - IDOR on backlog stories allows leaking of work package subject
The RbStoriesController calls Story.find(params[:id]) without scoping to the current project or visibility.
By causing an update to the Story with a subject longer than 255 characters, the update is rejected, which results in the original title being returned in the HTTP response.
Since user stories are mapped to work packages[1], this allows reading out the title of any work package just by providing the incrementing work package ID.
This vulnerability was reported by user posisec as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xfmm-g339-3x85
CVE-2026-27721 - Improper Authentication on OpenProject through /oauth/authorize via GET parameter "redirect_uri" when using mobile OAuth app
OpenProject permits the registration of custom URI schemes (e.g., openprojectapp://) for OAuth callbacks without enforcing PKCE (Proof Key for Code Exchange) or validating the exclusivity of the destination application (via Universal Links).
By intercepting this code, an attacker with access to the mobile device can exchange it for an access token (as the client is "Public" and has no secret), effectively hijacking the user's session and gaining full API access to their account
This vulnerability was reported by user wayward as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-w92f-h4wh-g4w4
CVE-2026-27722 - IDOR on OpenProject through /meetings/{meeting_id}/agenda_items/{id}/move_to_section via POST request
There is an Insecure Direct Object Reference (IDOR) in the MeetingAgendaItemsController#move_to_section endpoint. This allows an authenticated user to perform Meeting Agenda Pollution by moving their own agenda items into any meeting section of any other project.
While the initial agenda item is loaded from the authorized meeting context, the controller fails to validate that the target meeting_section_id belongs to the same project or a project where the user has permission.
This vulnerability was reported by user Herdiyan Adam Putra (herdiyanitdev) as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xw8w-4qxm-g9gv
CVE-2026-27731 - IDOR on OpenProject via PUT /work_packages/[workPackageId]/activities/[activityId]/toggle_reaction allows reader user to read internal comments
A missing permission check on the endpoint to add an emoji reaction to a comment allows an attacker to add an emoji reaction to internal comments, even if they do not have access to internal comments. To correctly display the information in the frontend, the server returns the complete internal comment with the added emoji reaction to the attacker. This allows the attacker by guessing the ID of an internal comment, to access those comments without the permission to see them.
This vulnerability was reported by user tuannq_gg as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-3qgp-q2x5-c4jw
CVE-2026-27733 - Authorization bypass via MCP endpoint
If the MCP server is enabled in the application, users that do not have access to enumerate Status or Types could access those resources without proper permission checks via the MCP server.
This vulnerability was reported by users noidont and syndrome_impostor as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-w9w6-f59w-89vj
CVE-2026-27817 - Missing boundary check allows users with Manage Agenda Items permission in one project to create Agenda Items in Meetings in other projects
When creating meeting agenda items, the code did properly check that the section an agenda item should be put into belongs to the meeting provided in the URL. This lead to a user with the Manage Meeting Agendas permission in one project to be able to add meeting agenda items to every meeting in the instance. Together with the response about the creation of the meeting agenda item, certain meeting details including
-
Status of the meeting
-
Creator of the meeting
-
Date and Time range of the meeting
No other details of the meeting information were exposed.
This vulnerability was reported by user sam91281 as part of the [YesWeHack.com OpenProject...
OpenProject 17.1.1
Release date: 2026-02-18
We released OpenProject OpenProject 17.1.1.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-26966 - Improper Access Control on OpenProject through /api/v3/queries via POST request allows unauthorized users to create project queries
A broken access control vulnerability exists in the /api/v3/queries endpoint that allows a normal authenticated user, without sufficient permissions, to create private project queries.
By reusing a valid request generated by an administrator and replacing the session cookie and CSRF token with those of a low-privileged user, the backend accepts the request and successfully creates the query.
This action should be restricted to authorized roles only. The issue demonstrates missing or improper authorization checks on query creation.
This vulnerability was reported by user slashx0x as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-5m66-2gm7-6jcc
CVE-2026-26968 - Improper Access Control on OpenProject instance through /api/v3/capabilities
The /api/v3/capabilities endpoint allows unauthorized enumeration of private project names and detailed permissions by specifying the built-in admin user ID as the principal.
While the API correctly prevents querying the capabilities of other users, the built-in Admin account remains resolvable.
Since projects use incremental values, and the built-in admin has visibility on all projects, this facilitates mapping of the entire openproject instance.
This vulnerability was reported by users syndrome_impostor and noidont as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-g62r-9rgf-h53q
CVE-2026-26969 - HTML Injection on OpenProject instance through project name
The application is vulnerable to HTML injection due to improper sanitization of user-supplied input for the project name.
An attacker can inject arbitrary HTML tags into the response, altering the structure of the page. and later while creating workpackages payload is executed.
This vulnerability was reported by user roro1702
as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-r4v5-h2fp-fhxf
CVE-2026-26970 - HTML injection on wiki updated mailer
An HTML injection vulnerability occurs in the wiki updated mailer function of OpenProject The application does not properly escape HTML tags, an attacker with invitation rights or users themselves when registrations are open can create a user name containing the HTML tags. If they then gain the permission to add or edit wiki pages, their author tag is not properly escaped in emails.
This vulnerability was reported by user yokokho as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jrhg-mx22-57rm
CVE-2026-26971 - IDOR on Hourly Rates Controller allows deletion of Hourly Rates on other projects
A project-scoped hourly rates update endpoint in the Costs module allows deleting a target user’s hourly rates across all projects by sending a crafted request that omits the user parameter. The request is authorized only against the URL project (:project_id), but the deletion query is not scoped to that project, resulting in cross-project broken access control (horizontal privilege escalation).
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xh2h-jfr6-3qhc
CVE-2026-26976 - HTML Injection via Email Field in User Registration Leading to Malicious Notification Email to Instance Owner (Admin)
When anonymous registration is enabled, an unauthenticated attacker can submit a malicious payload in the email field during registration attempt (/account/register). Even when the registration fails due to the free plan user limit (10 active users), the system sends a notification email to the instance owner/admin warning that the user limit is reached. This email reflects the malicious email payload unescaped in the body/subject/content, allowing HTML injection.
This enables phishing, content spoofing, or (in rare cases with permissive email clients) limited XSS-like behavior in the admin's inbox.
This vulnerability was reported by user pdowski as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-6m5j-mp2j-cgmm
CVE-2026-27006 - Path Traversal on OpenProject BIM Edition leads to Arbitrary File upload on BCF module, resulting in possible RCE when using file-based caching
An authenticated attacker with BCF module access can write arbitrary files to any writable directory on the server through a path traversal vulnerability in the BCF import functionality. For docker-compose based installations, this can be expanded to a remote code execution using cache deserialization.
This vulnerability was reported by user shafouzzz as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-4fvm-rrc8-mgch
CVE-2026-27019 - Path Traversal via Incoming Email Attachments Leads to Arbitrary File Write and RCE
When OpenProject is configured to accept and handle incoming emails, it was possible that an attacker could send an email with a specially crafted attachment that would be written to a predefined location in the filesystem. All files that can be written by the openproject system user could be written. This could even be evaluated to a Remote Code Execution vulnerability.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-r85w-rv9m-q784
Bug fixes and changes
- Bugfix: Documents: zooming in issue on iOS [#71023]
- Bugfix: Seeding in zh-TW fails [#71869]
- Bugfix: Default document types are recreated after every OpenProject update [#71877]
- Bugfix: External links in notification emails not captured [#71907]
- Bugfix: External links with encoded space in path lead to OpenProject home page [#71931]
- Bugfix: Error in meeting PDF exports if cover image file storage is broken [#71945]
- Bugfix: Last admin can delete themselves [#71980]
Contributions
A big thanks to our Community members for reporting bugs and helping us identify and provide fixes.
This release, special thanks for reporting and finding bugs go to Andreas H..
OpenProject 17.0.4
Release date: 2026-02-18
We released OpenProject OpenProject 17.0.4.
The release contains several bug fixes and we recommend updating to the newest version.
Below you will find a complete list of all changes and bug fixes.
Security fixes
CVE-2026-26966 - Improper Access Control on OpenProject through /api/v3/queries via POST request allows unauthorized users to create project queries
A broken access control vulnerability exists in the /api/v3/queries endpoint that allows a normal authenticated user, without sufficient permissions, to create private project queries.
By reusing a valid request generated by an administrator and replacing the session cookie and CSRF token with those of a low-privileged user, the backend accepts the request and successfully creates the query.
This action should be restricted to authorized roles only. The issue demonstrates missing or improper authorization checks on query creation.
This vulnerability was reported by user slashx0x as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-5m66-2gm7-6jcc
CVE-2026-26968 - Improper Access Control on OpenProject instance through /api/v3/capabilities
The /api/v3/capabilities endpoint allows unauthorized enumeration of private project names and detailed permissions by specifying the built-in admin user ID as the principal.
While the API correctly prevents querying the capabilities of other users, the built-in Admin account remains resolvable.
Since projects use incremental values, and the built-in admin has visibility on all projects, this facilitates mapping of the entire openproject instance.
This vulnerability was reported by users syndrome_impostor and noidont as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-g62r-9rgf-h53q
CVE-2026-26969 - HTML Injection on OpenProject instance through project name
The application is vulnerable to HTML injection due to improper sanitization of user-supplied input for the project name.
An attacker can inject arbitrary HTML tags into the response, altering the structure of the page. and later while creating workpackages payload is executed.
This vulnerability was reported by user roro1702
as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-r4v5-h2fp-fhxf
CVE-2026-26970 - HTML injection on wiki updated mailer
An HTML injection vulnerability occurs in the wiki updated mailer function of OpenProject The application does not properly escape HTML tags, an attacker with invitation rights or users themselves when registrations are open can create a user name containing the HTML tags. If they then gain the permission to add or edit wiki pages, their author tag is not properly escaped in emails.
This vulnerability was reported by user yokokho as part of the [YesWeHack.com OpenProject Bug Bounty program](https://yeswehack.com/programs/openproject), sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-jrhg-mx22-57rm
CVE-2026-26971 - IDOR on Hourly Rates Controller allows deletion of Hourly Rates on other projects
A project-scoped hourly rates update endpoint in the Costs module allows deleting a target user’s hourly rates across all projects by sending a crafted request that omits the user parameter. The request is authorized only against the URL project (:project_id), but the deletion query is not scoped to that project, resulting in cross-project broken access control (horizontal privilege escalation).
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-xh2h-jfr6-3qhc
CVE-2026-26976 - HTML Injection via Email Field in User Registration Leading to Malicious Notification Email to Instance Owner (Admin)
When anonymous registration is enabled, an unauthenticated attacker can submit a malicious payload in the email field during registration attempt (/account/register). Even when the registration fails due to the free plan user limit (10 active users), the system sends a notification email to the instance owner/admin warning that the user limit is reached. This email reflects the malicious email payload unescaped in the body/subject/content, allowing HTML injection.
This enables phishing, content spoofing, or (in rare cases with permissive email clients) limited XSS-like behavior in the admin's inbox.
This vulnerability was reported by user pdowski as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-6m5j-mp2j-cgmm
CVE-2026-27006 - Path Traversal on OpenProject BIM Edition leads to Arbitrary File upload on BCF module, resulting in possible RCE when using file-based caching
An authenticated attacker with BCF module access can write arbitrary files to any writable directory on the server through a path traversal vulnerability in the BCF import functionality. For docker-compose based installations, this can be expanded to a remote code execution using cache deserialization.
This vulnerability was reported by user shafouzzz as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-4fvm-rrc8-mgch
CVE-2026-27019 - Path Traversal via Incoming Email Attachments Leads to Arbitrary File Write and RCE
When OpenProject is configured to accept and handle incoming emails, it was possible that an attacker could send an email with a specially crafted attachment that would be written to a predefined location in the filesystem. All files that can be written by the openproject system user could be written. This could even be evaluated to a Remote Code Execution vulnerability.
This vulnerability was reported by user sam91281 as part of the YesWeHack.com OpenProject Bug Bounty program, sponsored by the European Commission.
For more information, please see the GitHub advisory #GHSA-r85w-rv9m-q784