-
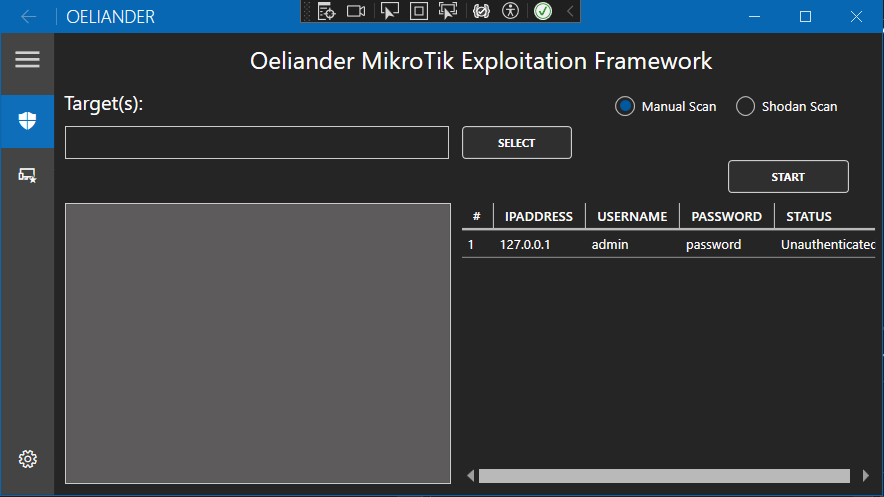
WinBox Auth Bypass Credential Disclosure (CVE-2018-14847)
-- Allows direct SSH into the vulnerable device using collected credentials
-- Allows for uploads to the target system
--Allows for root backdoor install using MikroTik options packageUNTESTED -
Shodan search integration
-- Allows for target collection and IP assessments using shodan
- F5 Big-IP Remote Code Execution Vulnerability [CVE-2023-46747]
- Juniper SRX Firewall Vulnerability [CVE-2023-36845]
- OpenFire Console Authentication Bypass Vulnerability [CVE-2023-3215]
- Remote Unauthenticated Code Execution Vulnerability in OpenSSH server [CVE-2024-6387]
- VMWare Aria Operations for Networks (vRealize Network Insight) unauthenticated RCE [CVE-2023-20887]
- VMWare ESXi RCE Exploit [CVE2021-21974]
- Atlassian Bitbucket Data Center Deserialization Vulnerability [CVE-2022-26133]
- ConnectWise ScreenConnect-AuthBypass-RCE [CVE-2024-1708][CVE-2024-1709]
MkCheck given an easy to use UI